High-risk online entertainment platforms depend on trust. A user may deposit money, buy credits, enter a paid feature, claim a reward, or request a withdrawal within minutes. If the payment flow feels unclear or unsafe, the whole product feels weak.
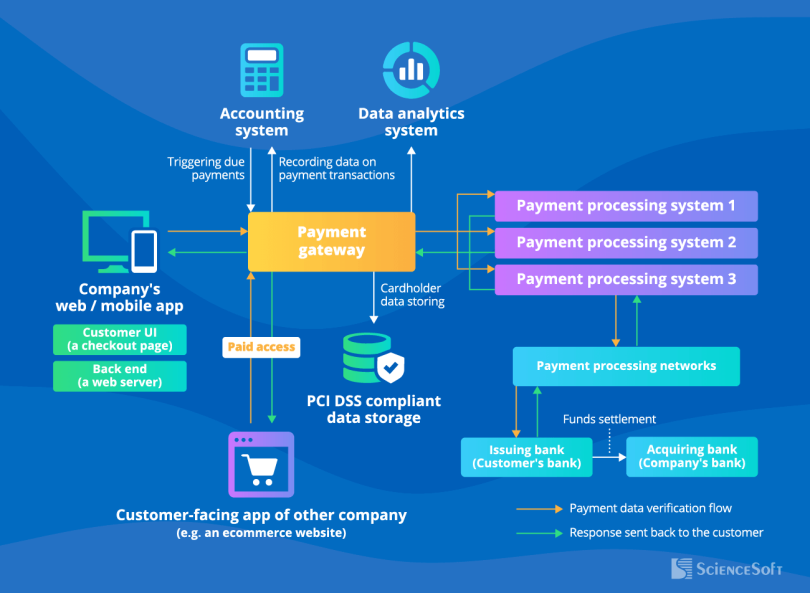
Java often sits behind these systems because it handles scale, security, and complex business rules well. A Java backend can process transactions, manage wallets, store logs, connect payment gateways, run fraud checks, and keep account balances consistent.
The main challenge is simple: money must never move in a vague way. Every payment needs a clear state. Every balance change needs a record. Every failed action needs a reason. Every user-facing number must match the backend truth.
This matters even more in entertainment spaces where speed and emotion meet. Gaming platforms, live-event apps, contest systems, and chance-based services often push users to act fast. Developers must slow down the risky parts without making the product feel broken.
A secure payment flow works like a guarded bridge. Users can cross it quickly, but the bridge still checks weight, direction, identity, and exit points. Good Java developers build that bridge with clear states, strong validation, safe storage, and full audit trails.
Start With A Clear Transaction State Machine
A secure payment flow needs clear states. A transaction should never move from “started” to “done” without passing through controlled steps. Each step should mean one thing and trigger one safe action.
A basic flow may include created, pending, confirmed, failed, expired, refunded, and settled. These states help the backend know what happened, what can happen next, and what should be blocked.
This matters for high-risk entertainment platforms because users often act quickly. A player may top up a wallet, join a live feature, or enter a fast game flow. If a platform includes instant formats such as aviator game online, the backend must keep payment states separate from game states so money logic stays clean and traceable.
Java developers should treat every transaction like a parcel with a tracking number. It must have an ID, source, destination, amount, currency, status, timestamp, and audit record. If the parcel gets delayed, returned, or rejected, the system should show exactly where it stopped.
A clear state machine prevents double charges, missing credits, false confirmations, and balance errors. It also makes support easier because the team can read the record instead of guessing what happened.
Validate Every Payment Before It Touches The Wallet
A wallet balance should not change just because a user clicked a button. The backend must first confirm that the payment is real, complete, and tied to the correct account.
Validation starts with basic checks. The system should confirm the user ID, transaction ID, amount, currency, gateway response, and payment status. It should also reject duplicate callbacks, expired sessions, mismatched amounts, and unknown references.
Payment gateways can send delayed or repeated events. A Java service must handle this safely. If the same confirmation arrives twice, the wallet should not receive credit twice. This is where idempotency matters. The same request should produce the same result, not a second payment action.
Developers should also separate external gateway status from internal wallet status. A gateway may say the payment succeeded, but the platform still needs to run its own checks before updating the balance.
A safe wallet works like a bank counter. The cashier does not add money until the note is checked, counted, and recorded. Backend code should follow the same rule.
Use Idempotency To Stop Double Charges And Double Credits
Payment systems receive the same event more than once. A gateway may retry a callback. A user may refresh the page. A mobile app may resend a request after a weak network connection. If the backend treats each repeat as new, money records can break.
This is why idempotency matters. The system should process one payment action only once, even if the same request arrives many times. The result should stay stable.
Java developers can support this with a unique idempotency key. The key may come from the client, gateway, or backend. Once the system accepts it, the service stores the key with the transaction result. If the same key returns, the backend sends the saved result instead of creating a new charge or credit.
This protects both the platform and the user. It prevents duplicate wallet top-ups, repeated withdrawals, double refunds, and confused support tickets.
Idempotency works like a stamp on a paper form. Once the form is stamped, the same form cannot create a second payment. The system can still show the result, but it should not repeat the money movement.
Keep Wallet Balance Changes Atomic
A wallet balance should change as one complete action, not as loose steps. If the system adds money, records a transaction, and updates the user account, all of that should succeed together or fail together.
This is where atomicity matters. A payment flow may touch several tables or services. It may update the wallet, write a ledger entry, notify the user, and mark the transaction as settled. If one part fails halfway, the system can show the wrong balance.
Java developers can reduce this risk with database transactions, row locking, version checks, and clear ledger design. The wallet should not rely only on a number stored in one field. It should have a record of every credit, debit, refund, and adjustment.
A strong ledger works like a bank passbook. The final balance matters, but the line-by-line history proves how that balance appeared. If a dispute happens, the team can follow the trail.
Atomic wallet updates protect users from missing funds and protect platforms from false credits. In high-risk entertainment systems, that precision is not optional. It is the base of trust.
Protect Payment APIs With Strong Authentication
A payment API should not trust a request only because it reaches the server. Every request must prove where it came from, who sent it, and whether the sender has the right to perform that action.
For user actions, the backend should check the active session, account status, device signals, and permission scope. For gateway callbacks, it should verify signatures, timestamps, IP rules where useful, and shared secrets or public-key checks. A fake callback should never be able to credit a wallet.
Java developers should also avoid placing sensitive payment logic directly in public controllers. The controller should receive the request, validate the shape, and pass it to a service layer that enforces business rules. This keeps the code easier to test and harder to misuse.
Rate limits matter too. Attackers may try to guess transaction IDs, abuse callbacks, or spam payment endpoints. A secure API should block noisy traffic before it reaches core money logic.
Authentication works like checking an ID at a guarded door. The system should not ask only, “What do you want?” It should ask, “Who are you, can I trust this request, and are you allowed to do this?”
Store Sensitive Payment Data With Care
Payment systems should store as little sensitive data as possible. A platform does not need full card details, private wallet keys, raw identity documents, or secrets sitting in plain text. The less it stores, the less it can leak.
Java developers should use trusted payment providers for card handling where possible. The backend can store safe references such as payment IDs, customer tokens, masked card numbers, and transaction status. It should not store full payment data unless there is a strict legal and technical reason.
Secrets need special treatment. API keys, gateway secrets, signing keys, and database passwords should live in secure secret managers, not inside source code, logs, or config files pushed to a repository.
Logs also need control. A helpful log can turn dangerous if it prints tokens, wallet addresses, email addresses, phone numbers, or full gateway responses. Logs should help debug the system without exposing the user.
Sensitive data is like cash in a locked drawer. Do not keep more than needed. Do not leave it visible. Do not let every service touch it.
Build Audit Trails For Every Money Event
A secure payment flow needs a full audit trail. The system should record every money event in a way that support, compliance, and engineering teams can understand later.
An audit trail should show who acted, what changed, when it changed, which service handled it, and why the system allowed it. It should include deposits, wallet credits, debits, refunds, withdrawals, failed attempts, manual adjustments, and gateway callbacks.
This record matters when users raise disputes. A user may say money left the bank but did not reach the wallet. Another may report a failed withdrawal. Without a clear trail, the support team must guess. Guessing is dangerous when money is involved.
Java developers should make audit logs tamper-resistant where possible. They should avoid silent balance edits and require reason codes for manual changes. Every adjustment should leave a visible footprint.
An audit trail works like CCTV for the payment system. It does not stop every problem, but it shows what happened when trust is questioned.
Monitor Fraud Signals In Real Time
High-risk platforms need fraud checks while the user journey is still active. A payment that looks normal at first can become suspicious when the system sees the full pattern.
Java services can monitor signals such as repeated failed payments, unusual deposit size, sudden withdrawal requests, many accounts using the same device, rapid wallet movement, and mismatched user details. One signal may mean little. Several together may show risk.
The system should not block every strange action at once. Some users simply travel, change phones, or make a larger payment than usual. A better design uses risk levels. Low risk can pass. Medium risk can need extra verification. High risk can pause the transaction for review.
Real-time monitoring works like a smoke detector. It should react early, but it should not flood the building with false alarms. Good rules need tuning, logs, and review.
Fraud checks protect more than company revenue. They protect honest users from stolen accounts, fake payments, and unsafe wallet activity. In payment systems, security is part of the product experience.
Make Withdrawals Clear, Slow Enough, And Traceable
Withdrawals need stricter control than deposits. A deposit brings money into the platform. A withdrawal sends money out, often to a bank account, wallet, or external payment route. If the system makes a mistake here, recovery can be hard.
Java developers should build withdrawal flows with clear checks. The system should verify the user, balance, withdrawal method, account status, risk score, and pending disputes before funds leave. It should also block withdrawals that exceed limits or fail identity rules.
Speed matters, but instant withdrawal is not always the safest choice. A short review window can protect users from account theft and give fraud systems time to detect strange behaviour. The key is to explain the delay clearly.
Users should see each withdrawal state: requested, under review, approved, processing, completed, failed, or reversed. They should not have to guess where their money is.
A safe withdrawal flow works like a bank transfer with a tracking slip. The user knows the amount, route, status, and expected next step. That clarity reduces support pressure and protects trust.
Test Payment Flows Against Failure, Not Only Success
A payment flow is not ready just because the happy path works. Real users face weak networks, closed tabs, repeated clicks, delayed callbacks, expired sessions, gateway errors, and failed bank confirmations. The backend must handle those cases cleanly.
Java developers should test deposits, withdrawals, refunds, duplicate requests, timeout events, partial failures, and manual reviews. Each test should answer one question: does the system still protect the user’s money when something breaks?
Failure tests should also check messages shown to users. A vague error like “something went wrong” creates fear when money is involved. A better message explains whether the transaction failed, is pending, or needs support.
Automated tests can cover core rules. Manual testing can check the full user journey. Load testing can show whether payment states remain stable during traffic spikes.
A secure payment system should behave well under stress. Anyone can build a flow that works on a calm day. Trust comes from building one that stays correct when the road gets rough.
Secure Payment Flows Are Built On Proof
Secure payment flows depend on proof at every step. The system should prove who made the request, what amount moved, which state changed, and why the backend allowed it.
For Java developers, this means building payment logic with clear transaction states, strict validation, idempotency, atomic wallet updates, strong API checks, careful data storage, and full audit trails. Each part protects the same goal: money should move only when the system can explain it.
High-risk online entertainment platforms need this discipline more than most products. Their users often act fast, emotions run high, and disputes can grow quickly. A weak payment flow can damage trust, even if the rest of the platform works well.
The best backend feels calm. It does not guess. It does not hide. It records, checks, confirms, and explains. That is how secure payment systems protect users, support teams, and the business behind the platform.